
"I don't think we can use your load balancer, because it's not a reverse proxy..." said the slightly confused reseller.
Which got me thinking, maybe I should write a blog about reverse proxy, and the difference between a reverse proxy server and a forward proxy server!
What is a reverse proxy server?
Wikipedia describes a reverse proxy server as:
"A reverse proxy is a type of proxy server that retrieves resources on behalf of a client from one or more servers. These resources are then returned to the client like they originated from the proxy server itself.[1] So a reverse proxy is an intermediary for its associated servers to be contacted by any client."
But I think I have a far simpler description: reverse proxy server = Layer 7 load balancer.
It kind of shows the irony in the resellers comments about our load balancer not being a reverse proxy doesn't it?! Clearly any Layer 7 load balancer is a reverse proxy.
So what is a forward proxy server then?
Wikipedia describes a forward proxy server as:
"A proxy server is a server (a computer system or an application) that acts as an intermediary for requests from clients seeking resources from other servers. A client connects to the proxy server, requesting some service, such as a file, connection, web page, or other resource available from a different server and the proxy server evaluates the request as a way to simplify and control its complexity."
But again I think I have a far simpler description: forward proxy server = web filter.
Quite often you will use a load balancer in front of a bunch of web filters, and we specialize in these kind of large scale deployments for all the big web filter vendors.
When is a load balancer NOT a reverse proxy?
Technically, the only mode on a load balancer that is a real Reverse Proxy is Layer 7 mode. Whereas all Layer 4 load balancing modes such as NAT, DR and TUN are nothing like a reverse proxy. Instead, with Layer 4 load balancing, the clients are effectively talking directly (transparently) to the backend servers.
Is a reverse proxy more secure than a Layer 4 load balancer?
The short answer is NO!
A reverse proxy is still sending all of your requests to the real servers, so any application security issues are still easily exploitable.
This is one of the many reasons why Microsoft dropped TMG; because it was effectively a pointless solution. The one semi-useful feature on TMG to most IT Managers was the ability to allow single user sign-on (SSO) for multiple applications. However, Microsoft rightly decided that actually SSO in itself is a serious security risk (single bastion host on the edge of the network with access to all of the passwords on the network, anyone?!).
But back to the thing I really hated about TMG. Forcing you to use a demilitarized zone network (DMZ)! Arrrggghhhh!!!!!!
Look in an enterprise network, a DMZ is a potentially sensible thing to use, possibly even essential. Sean Wilkins wrote a good description of DMZs here.
BUT with TMG you are forced to put yet another DMZ inside your original DMZ for no reason!
The 'too many DMZs problem' happens a lot with load balancer installations as well, every single server cluster ends up in its own DMZ. Because someone thought it was a good idea...
Some people even think that the load balancer won't work unless it is the default gateway for your servers with at least two subnets....
So what happens when someone moves a perfectly good application cluster, from its perfectly good and well designed DMZ, behind a load balancer? Everyone loses access to the new and unnecessary DMZ! And who are they going to blame?
Yes, that's right the load balancer vendor :-).
Please, please, please, for the sanity of your engineers, consider the idea of putting your load balancers in one-arm mode, and NOT a two-arm DMZ.
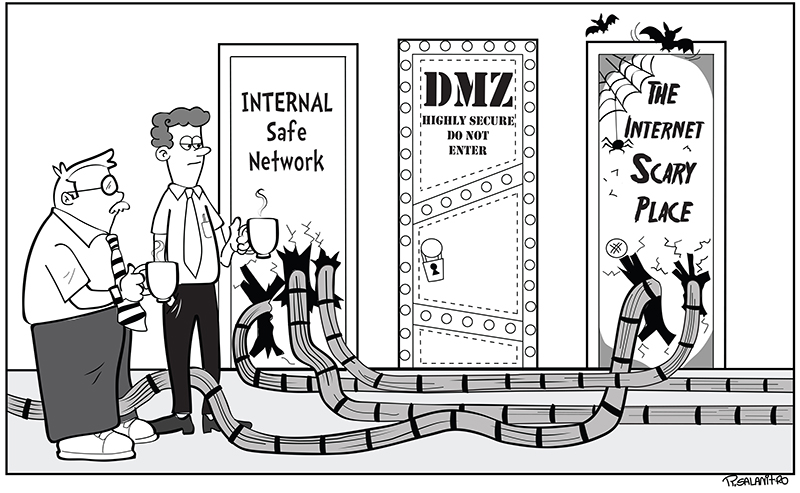
The cartoon above illustrates the classic example of what engineers do when faced by a DMZ access problem - run a cable to the other side. I've seen this happen a thousand times.
And there you have it. Rant over. Feel free to leave me a comment and tell me I'm talking rubbish (as usual), thanks.
















