Insights from the load balancer experts
Layer 7 load balancing: The complete guide to boosting application performance
Optimizing data storage: Using content-length headers to solve the 'small objects problem'
The ultimate guide to Global Server Load Balancing (GSLB): Benefits, uses, and configurations
Finally, a simple way to convert MaxMind GeoIP Database files to the legacy DAT format!

Load balancing Omnissa Horizon: Choosing the right UAG design
The Citrix NetScaler vulnerability crisis: When your load balancer becomes a liability

Breaking up with the BIG-IP: F5 iSeries load balancer alternatives

Hardening HashiCorp Vault with load balancing for always-on security

What's the best cloud load balancer? AWS, Azure, GCP, Cloudflare, or a third-party alternative?
When is an ACL not an ACL? When it's an HAProxy ACL...
NetScaler troubleshooting: The complete guide to solving on-prem LAS Offline Activation headaches

Architecting the perfect Christmas? A Highly Available light display!
How to load balance a MariaDB Galera Cluster for performance and HA using LVS & Ldirectord

Multi-AZ resilience: Why the recent AWS outage shows you need it
Hardening the edge: Essential security lessons for F5 users following the recent breach
Loadbalancer.org Enterprise: A technical guide to Layer 7 Manual Configuration
Using Grafana Loki with HAProxy for log aggregation
Layer 7 load balancing: The complete guide to boosting application performance
Optimizing data storage: Using content-length headers to solve the 'small objects problem'

IPv6 and Loadbalancer.org: Finally making friends with those impossibly long addresses
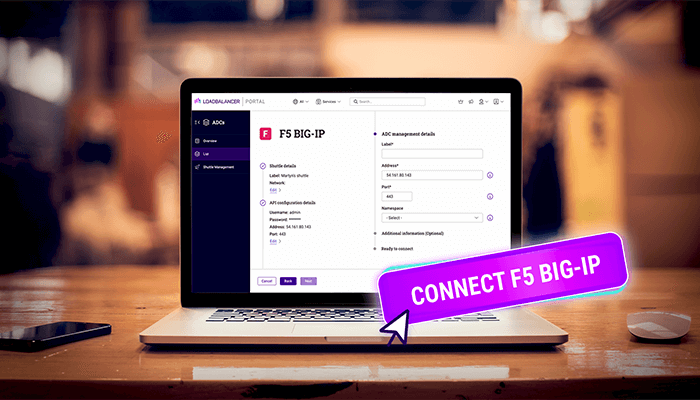
How to set up and manage an F5 in the ADC Portal

Load balancing Weka is no longer optional — the new normal is 100X faster
The complete guide to Layer 4 load balancing: How it works, when to use, and how to configure

Unlocking the power of Endurance: A beginner's API guide for smarter load balancing
Building Endurance: A load balancer with a clear purpose
Microsoft NLB is finally going End of Life — so what next?!