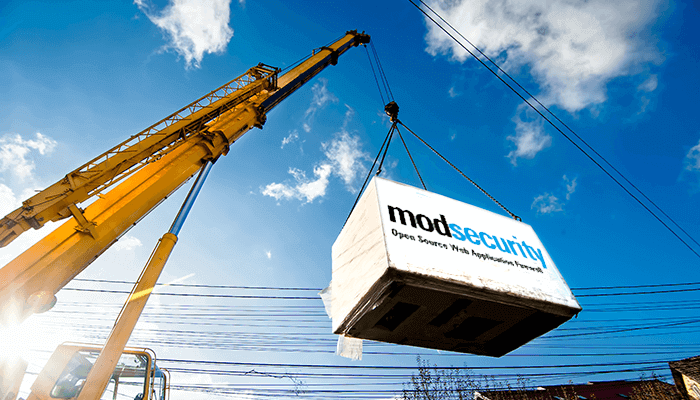
WAF
Protect your web applications from threats like SQL Injection and XSS using our integrated Web Application Firewall. Learn how to configure the OWASP Core Rule Set, train your WAF, and leverage this crucial layer of defense for security and PCI compliance.