Benefits of load balancing Microsoft IIS
Load balancing Microsoft Information Services (IIS) provides these key benefits:
- High Availability (HA): The distribution of traffic across multiple servers ensures that if one IIS server fails (a hardware or software issue), the load balancer automatically detects the failure and redirects all traffic to the remaining healthy servers (automatic failover). This prevents a single point of failure and ensures your application remains continuously available to users. Load balancers continuously check the health of the backend IIS servers. If a server is slow, unresponsive, or fails a specific health check, it’s temporarily taken out of the server farm until it recovers, preventing users from being served by an unhealthy machine. The redundant architecture provided by load balancing significantly increases the overall resilience of the web platform, minimizing the impact of potential hardware or software issues
- Improved performance: Load balancing distributes incoming client requests across multiple IIS servers (often called a server farm). This prevents any single server from becoming overwhelmed, ensuring no server operates at capacity while others are idle, thus maximizing resource utilization. By sharing the workload, the system can handle a greater volume of requests (higher throughput) and respond faster to individual user requests (lower response time), leading to a better user experience.
- Scalability: As traffic grows, its easy to add more IIS servers to the server farm behind the load balancer without having to take the entire system offline. This allows for horizonal scale out which is more cost-effectively than upgrading a single, powerful server.
About Microsoft IIS
Microsoft Internet Information Services (IIS) is a high performance, flexible web server created by Microsoft for use with Windows. In order for web sites to remain available, IT managers will need to configure IIS server load balancing.
Loadbalancer.org supports Microsoft IIS with all common load balancing methods, incorporating numerous modifications and customisations to suit your requirements and can be deployed physically, virtually or in the cloud. Whatever your preference, we’ll ensure that your deployment is suited for your environment.
Microsoft’s Enterprise solutions are at the heart of businesses everywhere. Loadbalancer.org is officially certified for all of Microsoft’s key applications which you can find here. More details on the Microsoft IIS components, how it works, and prerequisites for load balancing can be found in our deployment guide, available to view below.
Why Loadbalancer.org for Microsoft IIS?
Loadbalancer’s intuitive Enterprise Application Delivery Controller (ADC) is designed to save time and money with a clever, not complex, WebUI.
Easily configure, deploy, manage, and maintain our Enterprise load balancer, reducing complexity and the risk of human error. For a difference you can see in just minutes.
And with WAF and GSLB included straight out-of-the-box, there’s no hidden costs, so the prices you see on our website are fully transparent.
More on what’s possible with Loadbalancer.org.
How to load balance Microsoft IIS
The load balancer can be deployed in 4 fundamental ways: Layer 4 DR mode, Layer 4 NAT mode, Layer 4 SNAT mode and Layer 7 Reverse Proxy (Layer 7 SNAT mode).
For IIS, Layer 4 DR mode, Layer 4 NAT mode or Layer 7 Reverse Proxy are recommended.
Virtual service (VIP) requirements
Layer 4 DR VIP requirements:
Layer 4 NAT VIP requirements:
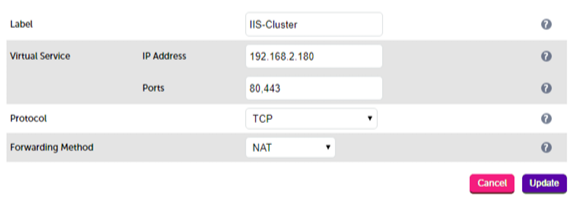
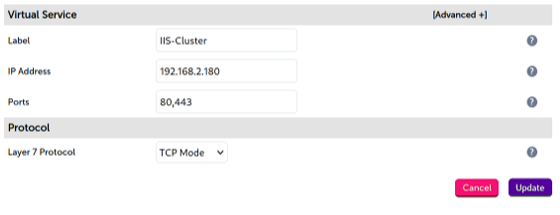
Layer 7 Reverse Proxy VIP requirements:
Port requirements and protocols
| Protocol | Port | Load balancing methods |
|---|---|---|
| HTTP | 80 | Layer 7 SNAT (Recommended) Using Reverse Proxy mode is the easiest and most flexible load balancing method, offering advanced URL switching, cookie insertion and WAF capabilities.Layer 4 DR Direct Routing has the advantage of being fully transparent and seriously fast but requires solving the arp problem.Layer 4 NAT Traditional NAT mode gives easy to implement fast and transparent load balancing but usually requires a two-arm configuration (two subnets). |
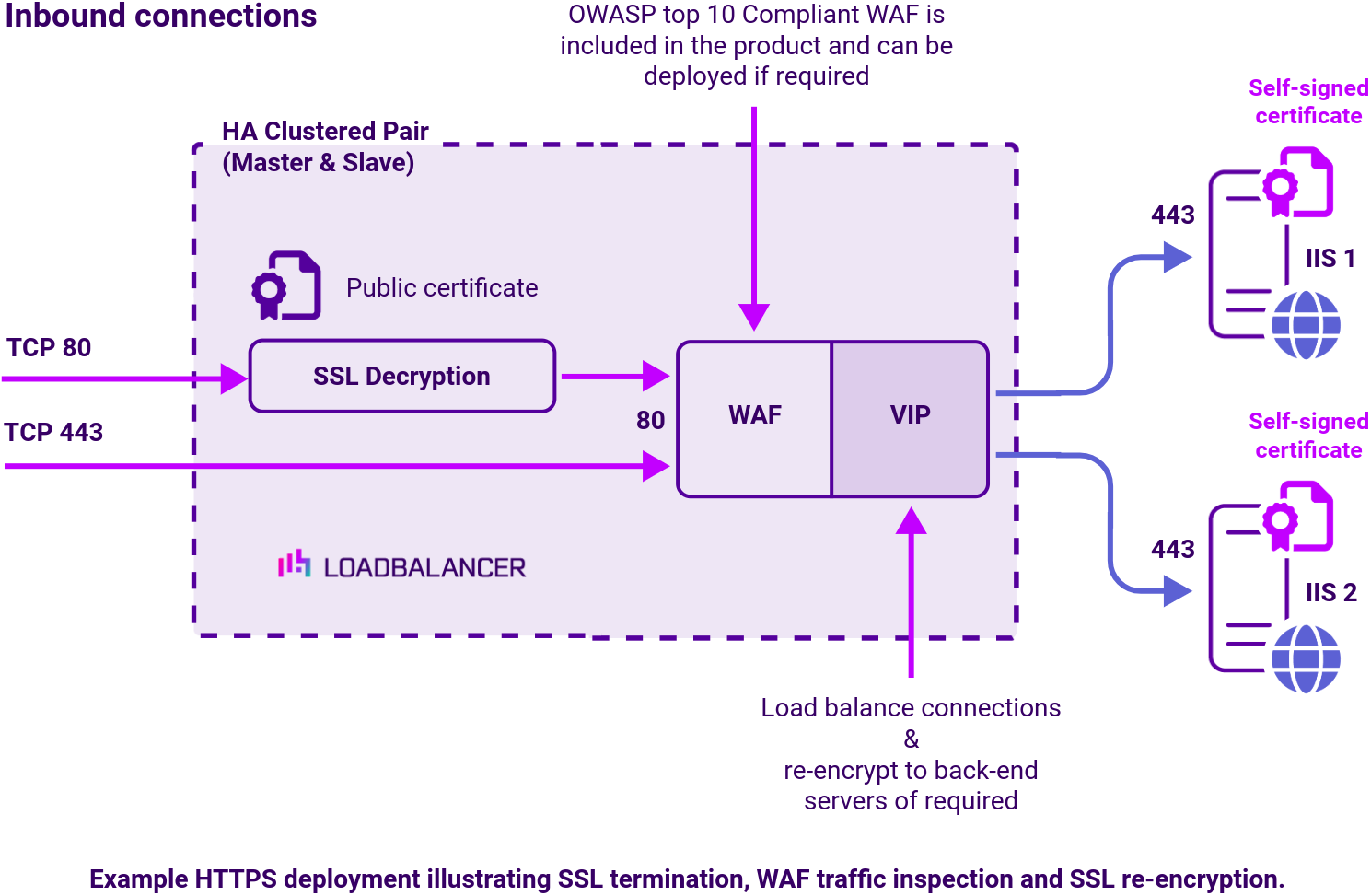
| HTTPS | 443 | All load balancing methods can be easily configured for SSL Pass-through.This has the advantage of being fast, secure and easy to maintain. Identical SSL certificates will need to exist on each of your backend servers for pass-through security.SSL Termination or off-loading must be used when advanced Layer 7 functionality such as cookies or URL switching is required. You can also implement SNI if you have multiple domain certificates one one public IP address. Optional re-encryption is also available between the load balancer and IIS. |
| FTP | 20,21 | All load balancing methods can be easily configured for FTP. However the original design of FTP did not work well with firewalls so it was modified to add a special PASV (Passive) mode. If you are load balancing FTP we recommend that you configure PASV on the FTP server, or use Layer 4 NAT mode which handles the issue automatically. |
| SFTP | 21 | All load balancing methods can be easily configured for SFTP. |
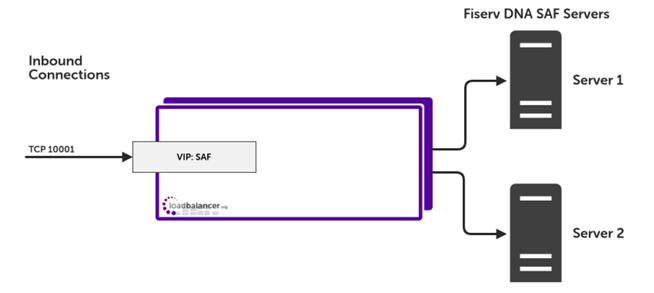
Load balancing deployment concept