JetNEXUS (EdgeNEXUS) is a great UK based vendor of application delivery controllers. The company initially started way back in 2004, selling a gzip compression plugin for Microsoft IIS 4. Then in 2007 they did a deal to re-badge the excellent Zeus ZXTM application delivery controller. This was a great deal for them as they could sell the high-end ZXTM traffic manager and at the same time gradually add features to their own reverse proxy load balancer.
Everything changed in 2012 just after RiverBed bought the Cambridge startup Zeus (@ 10x Revenue i.e. 100 x EBITDA!). Riverbed dropped the JetNEXUS OEM deal and promptly went on to destroy the Zeus brand.
So, JetNEXUS was forced to go it alone with the ALB-X and since then they've been hard at work turning it into a fully featured application delivery controller.
JetNEXUS have a particular niche in the channel for customers who don't need all the features of an F5 but do need something similar to iRules (JetNEXUS call it flightpath).
However, much like the trouble Coyote Point Systems had with the channel — they sometimes struggle communicating this middle of the market (almost an F5) message.
So, what do I think of the current JetNEXUS product?
Actually, I quite like it. It's pretty simple to install and do the basic configuration. As the default mode is a full reverse proxy you can quickly configure a virtual service and add a couple of real servers.
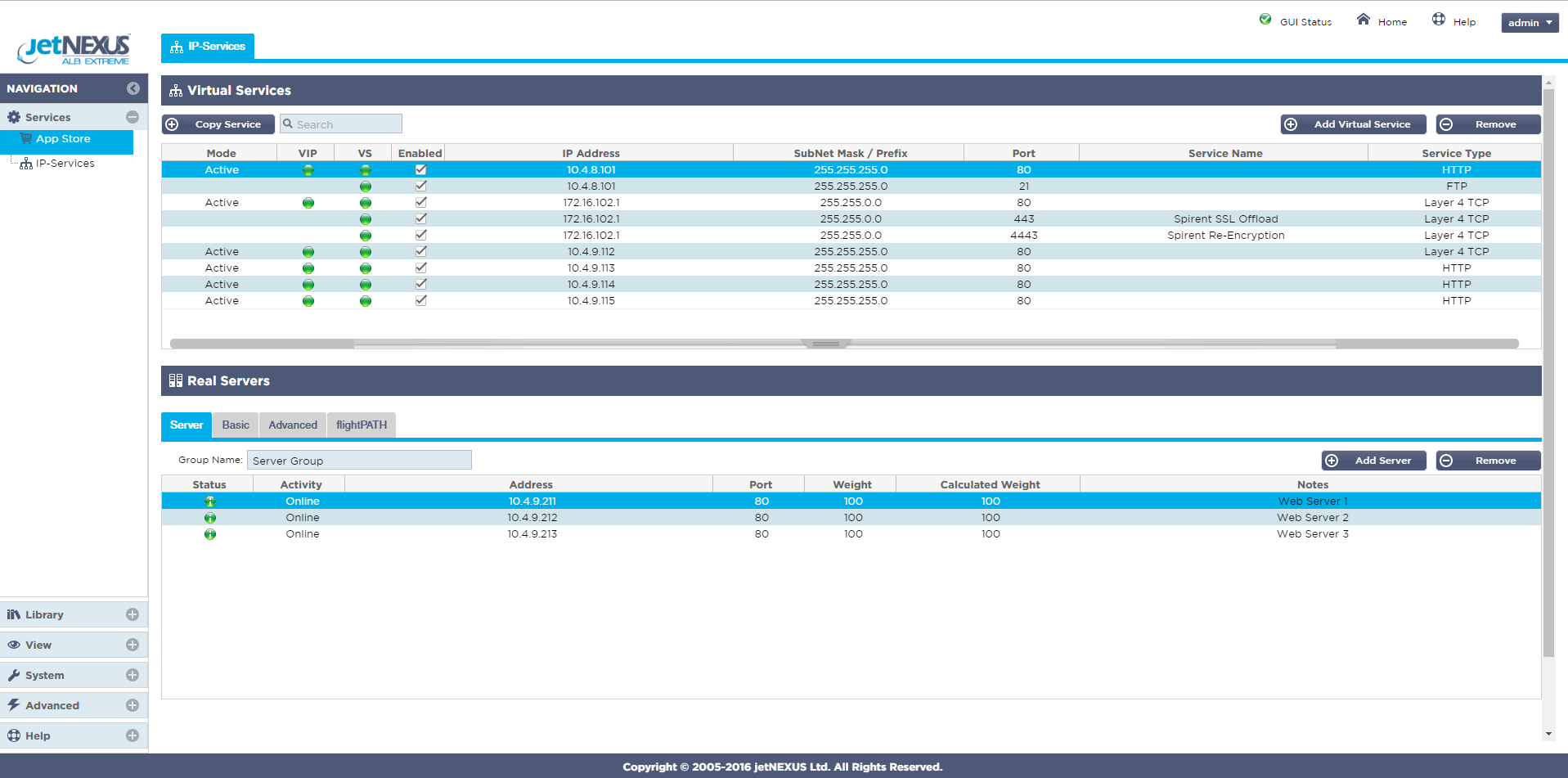
JetNEXUS has a nice clean interface but lacks flexibility...
It is very similar to Barracuda Networks in that you can only assign a single port per virtual server or backend. I find that annoying, even if you can create more virtual servers with the same IP address — it's not very flexible.
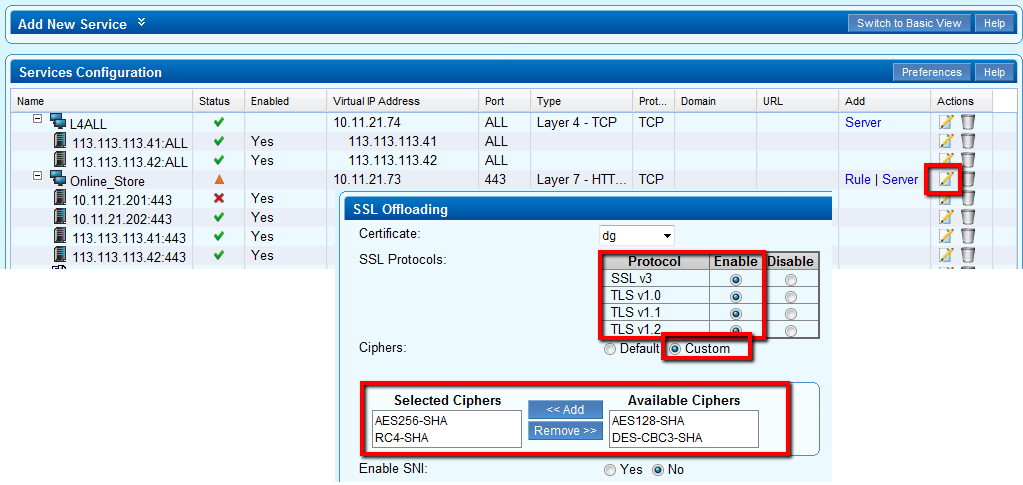
Barracuda ADC just like JetNEXUS, only allows you to specify ONE port per VIP...
The Kemp and Loadbalancer.org products are definitely much more flexible for multi-port configurations. And I'm sure the KEMP developers are still working on it being feature complete before worrying about how it looks :-)
KEMP has completely updated its look...with blue instead of yellow!
With JetNEXUS the standard health checks are easily available from a drop down list, although I find it strange that the load balancing method is directly linked to the health check - you can't mix and match. The Layer 4 is handled by the open source LVS just like all the other vendors. Barracuda & Loadbalancer.org use HAProxy for layer 7 services, while Kemp and JetNexus use their own proxy engine.
I definitely like the real times graphs in the JetNEXUS product, probably the best looking of the bunch. Barracuda & Kemp graphs although not as pretty — are probably a bit more flexible.
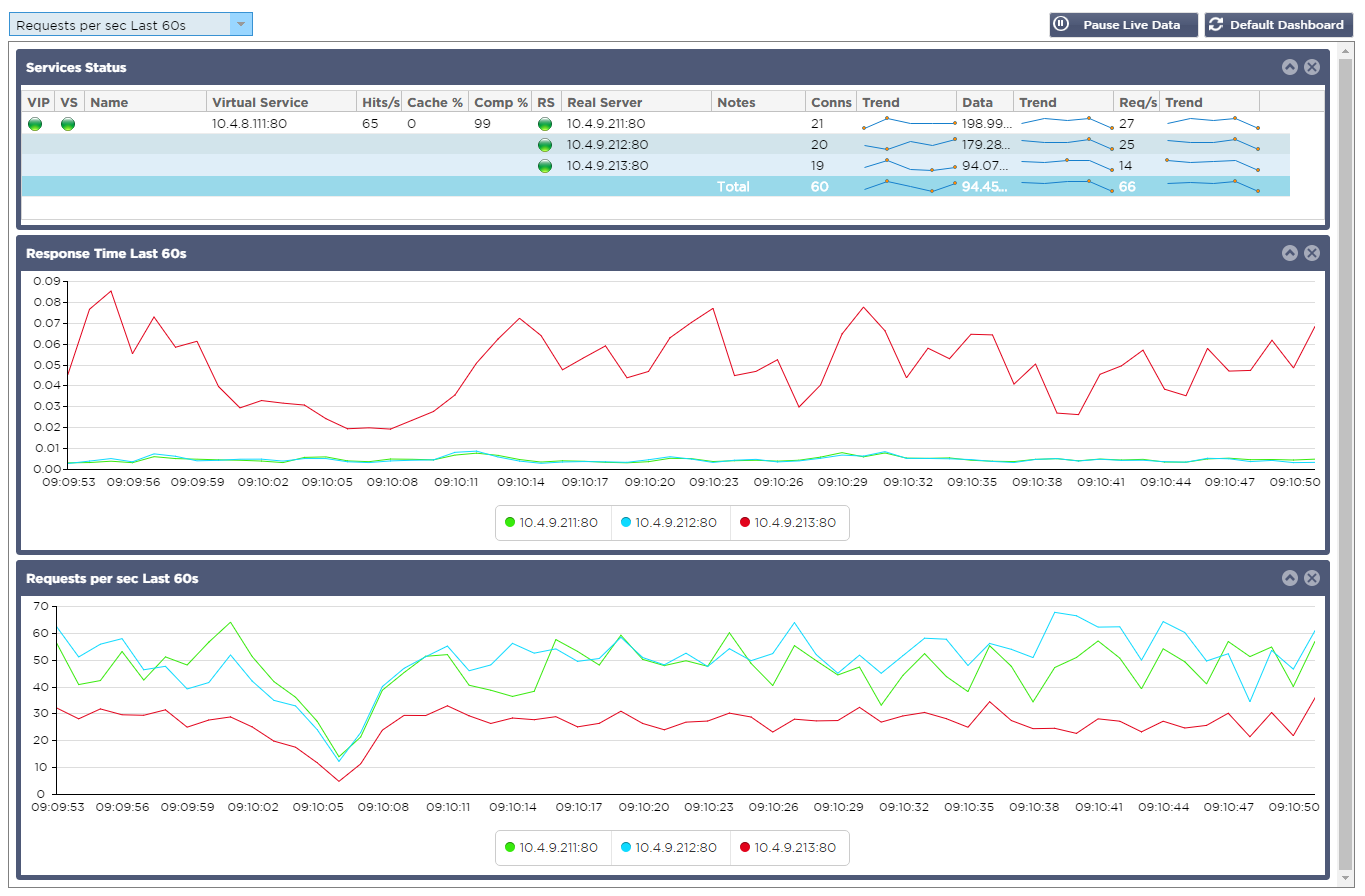
Look pretty graphs on the JetNEXUS...that move!
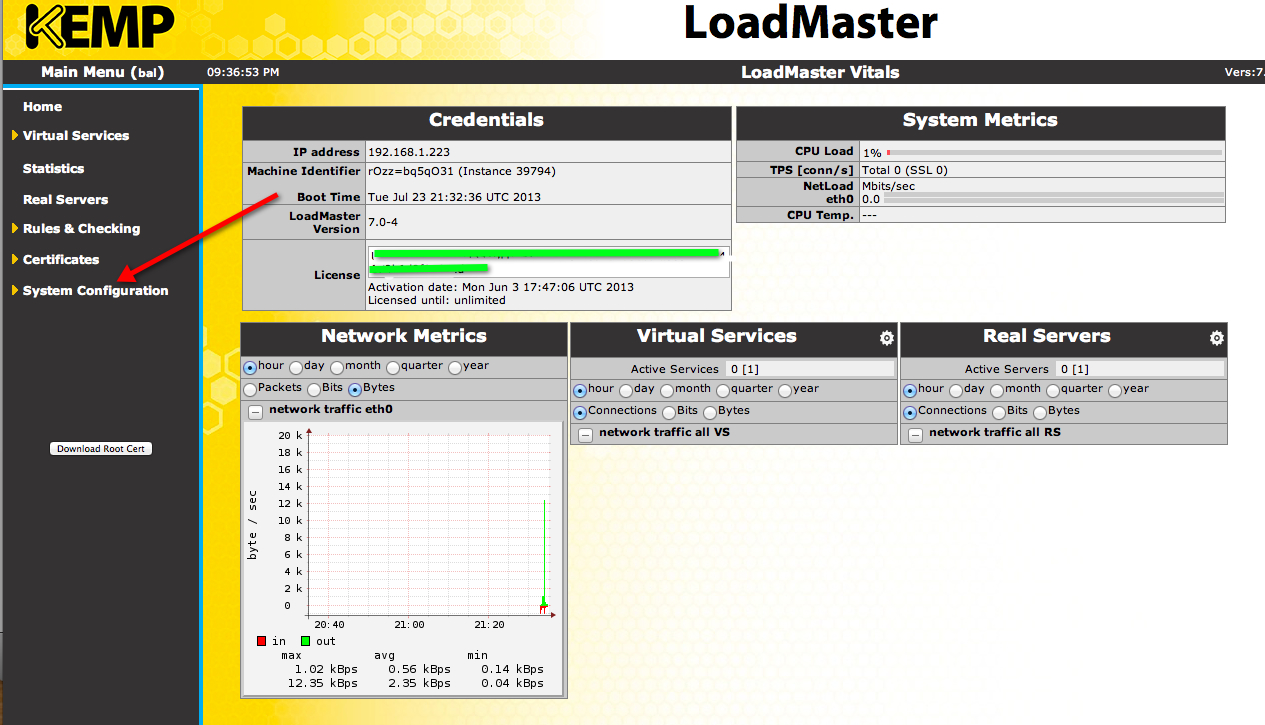
The KEMP graphs are ugly but very customisable....
How flexible is the JetNEXUS?
The most common advanced functionality that you might be looking for is access control lists, redirection and URL context switching. All four vendors support this to a varying fashion. JetNEXUS needs a customised FlightPath rule for each action you wish to take. Once the rules are created this makes it easy but personally I find it overly complicated and prone to error. KEMP and Barracuda go for the 'let's have every option under the sun' - which while feature complete (i.e. they copied the F5 feature set) — it is also very confusing and prone to error. Here at Loadbalancer.org we've kept it nice and simple:
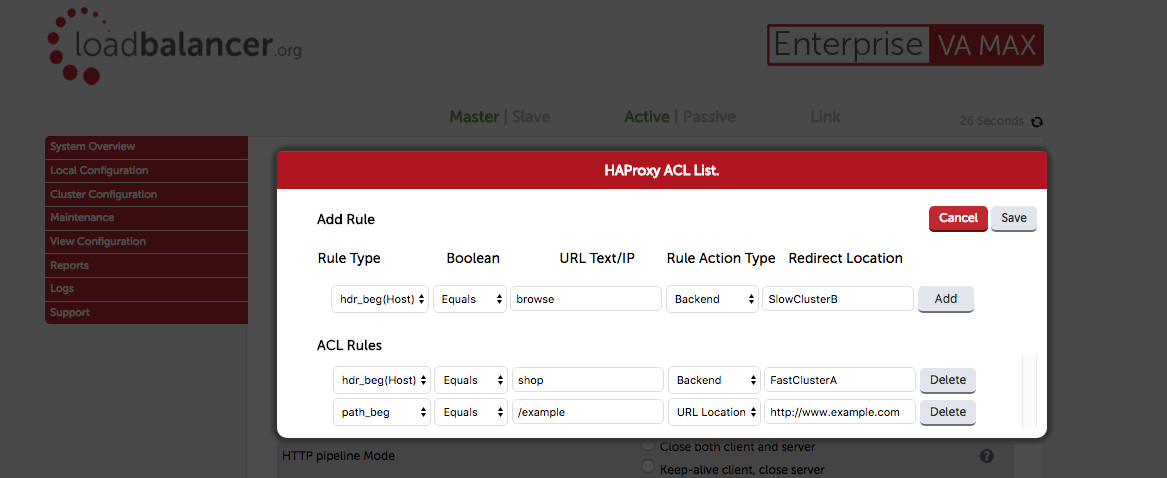
Loadbalancer.org ACLs — how simple is that?
Whereas KEMP has a 30 page manual to describe regex configuration and 6 separate configuration dialogues:
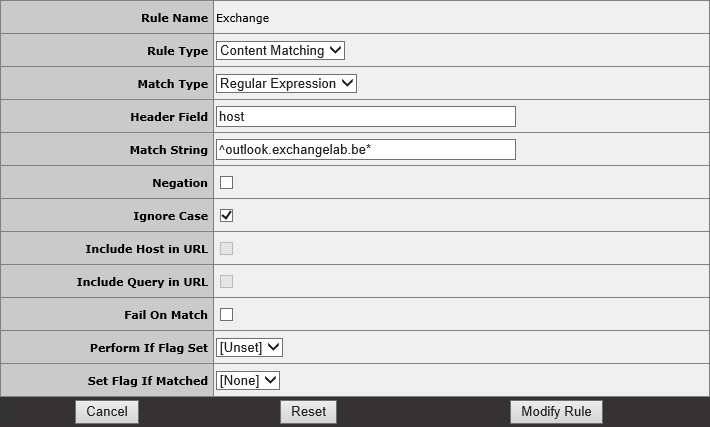
I think I prefer JetNEXUS FlightPath to KEMPs regex hell...
Who uses this stuff anyway?
Well to be honest — most people don't. But for those that do:
90% just just require simple ACLs, URL redirects, IP blocking and force to HTTPS functionality.
The remaining 10% may want to actually use these rules to create specific behaviours for different types of application traffic, such as giving priority to certain customers, slowing down hackers or creating complex disaster recovery scenarios.
F5 and Loadbalancer.org have always supported this with unlimited manual backend configuration support. Simply define your advanced backend pools with whatever features you require. Then use the web interface to select those named backends based on ACL rules.
KEMP has recenly added full graphical support for multiple-backends which they call 'sub-VS' or 'sub virtual services'. KEMPs implementation is again ugly but fully featured and very flexible. Barracuda and JetNEXUS don't support it at all.
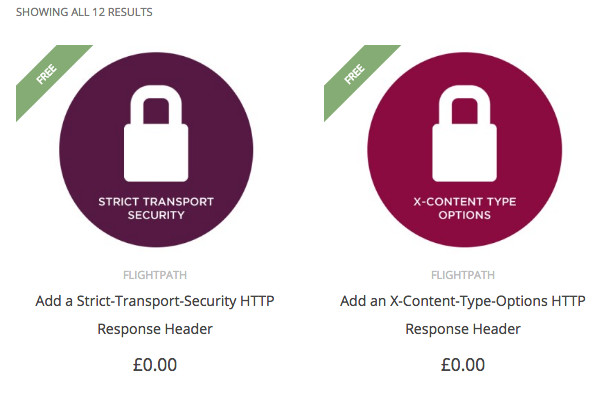
So what does FlightPath do that other solutions don't?
Well for starters JetNEXUS has a shop! Where you can download each individual FlightPath rule or server templates (such as Exchange):
But more importantly, JetNEXUS try to compete with F5 for full application visibility. FlightPath can be scripted to inspect all of the traffic in both directions — which is quite impressive. KEMP has very limited similar functionality in the core ADC.
But is it just me that thinks, anything as slow and complex as inspecting every body response for credit card details should be done in a WAF? Certainly if a customer wants to blank out credit card details in a response then on a Loadbalancer.org appliance, you would just add a simple one line rule for the WAF configuration.
If we had WAFs 10 years ago would F5 even bother having body inspection as a feature? I know Willy Tarreau has already said he will never support it in HAProxy.
How does JetNEXUS performance compare?
I'm sure its great, as I've said many times before — you really don't need to worry about a load balancers performance on modern hardware.
What about price and market segmentation strategy?
Barracuda Networks, KEMP Technologies and JetNEXUS all have fairly similar price structures. Basically it costs more if you want more bandwidth or more features. In contrast, Loadbalancer.org has a small deployment / large deployment price split.
They all have slight differences though:
- Barracuda is effectively a rental agreement as it is NOT a perpetual licence.
- KEMP does have a perpetual licence but advanced features are only available if paying annually for them through the 3 tier support contract.
- JetNEXUS is a perpetual licence but you must pay extra for the advanced features up front.
- Loadbalancer.org gives all features and unlimited performance with the perpetual licence. However, the low price point R20, is restricted to 5 clusters of 4 servers.
So isn't this comparison a bit too subjective?
Yes, but then I'd like to think I'm qualified to have an opinion and although I'm obviously biased — you might be interested in my slightly aggressive conclusions.
All 4 load balancers (application delivery controllers) that I have compared in this review are perfectly capable. They have different strengths and weaknesses but no obvious show stoppers to make you choose one over another.
They are all commodity products, based on a 20 year old F5 design....
What is important when you choose a load balancer vendor?
Well I think you need to consider 5 things:
- Price — never forget that one!
- What is the primary focus and strategy of the vendor?
- What is the technology platform risk?
- What is the support service like?
- How popular/strong is the vendor?
But which load balancer is the best?
In order to reach conclusions about the vendors and products, let's consider each of the 5 points above:
Barracuda Networks
A large corporation focused on security. They have a large customer base that was created from the original product - a cheap and effective web filter. The now have lots of commodity products based on open source technology. The Barracuda ADC can be cost effective but they have a distinct lack of focus compared to the other products they sell. The clear aim of the vendor is selling boxes and making money. The technology is open source so minimising risk but implementation is weak, unfocused and in my opinion, not trust worthy. I can't imagine the support is that good and the market penetration is weak. It is the one vendor I consistently hear horror stories about from ex-customers of theirs.
JetNEXUS
An agile company very focused on development of complex technology, clear sense of direction and target market of ex-F5 customers. They also have some interesting client side and edge of network acceleration tools in development stages. The product itself has a quality look and feel compared to the others in the market. However while they use Linux and LVS, the vast majority of the product is highly proprietary — and building a complex product from scratch involves high risk. They are at the mercy of a small distribution channel and I feel they also need to invest more effort in customer support.
KEMP Technologies
A fast growing company based on a tightly focused group of application delivery products. Largely open source but with proprietary Layer 7 engine. Driven by venture capital, the focus is on adding every feature that an F5 has got now and to make it look pretty later. Price seems to be rising rapidly at the moment — especially when features and bandwidth are based on the higher end products and support packages. They sometimes have trouble with the channel and support issues but in general they are a very good choice — I can't see you getting fired for buying one!
Loadbalancer.org
Focused on traditional application delivery much like Kemp — but with a strong emphasis on high-availability and customer support. The technology is strong and the risk is negligible, as the product is closely tied to the open source community. The rapidly growing customer base, while not as large as Kemp is very vocal in its support of the product range. With development focused on security and reliability, advanced features may take longer to appear than the other vendors. WAF and GSLB support have only recently been added and may need time to mature.
Where should you go next for slightly less biased information?
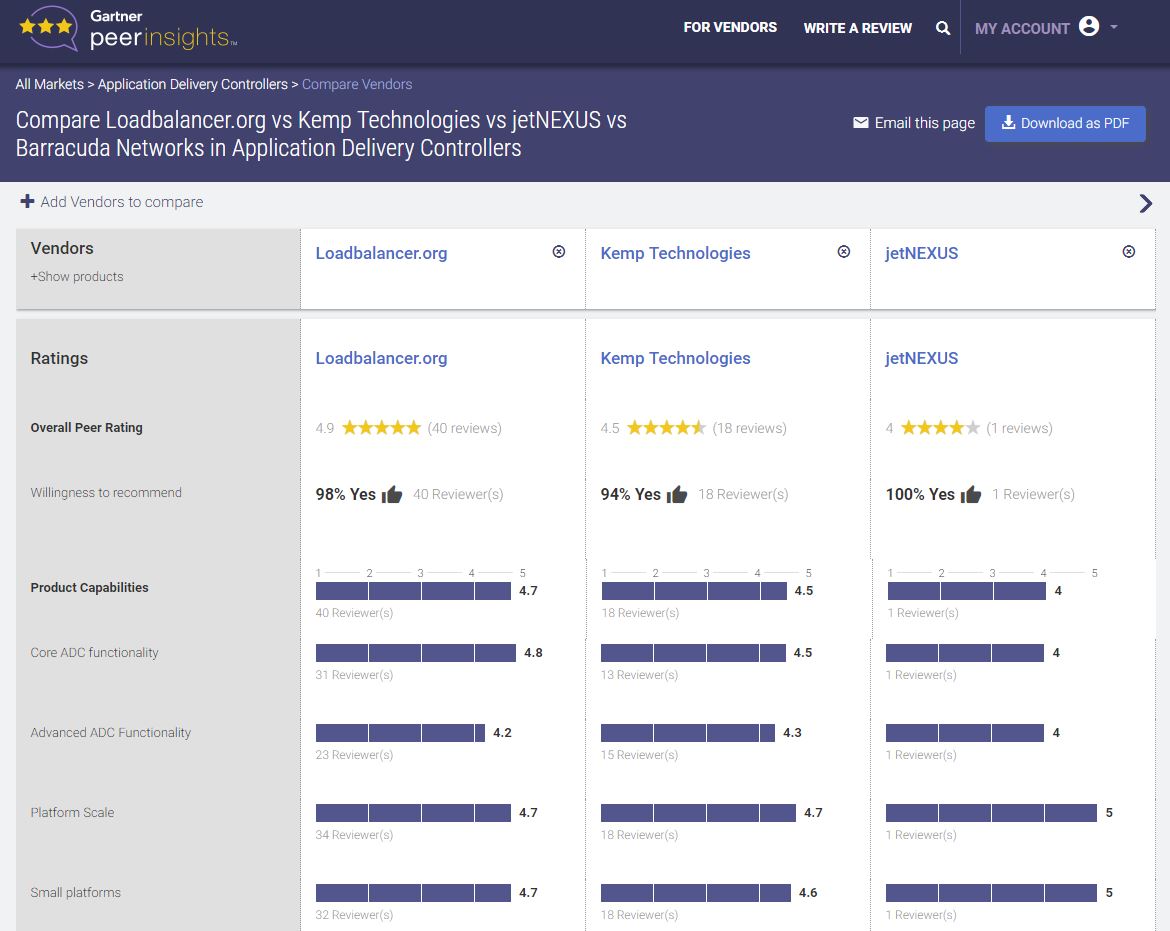
Well personally, I've never been too impressed with how impartial Gartner advice has been — with the so called Magic Quadrant. However, after receiving a lot of criticism, they do seem to be changing course. The new market guide to application delivery controllers takes a lot more account of how people are actually using these devices in production.
Gartner now also take into consideration real customer accounts of the purchasing and deployment process. You can check directly what customers having been telling Gartner about Loadbalancer.org, JetNEXUS, Barracuda Networks and Kemp Technologies on the new Peer Insights platform.